What can employees manage from the Security Settings page on their personal account?
The Security Settings page allows employees to control the security of their account. They can control their login credentials, session management (where they are logged in) and also see a log of their activity.
Change Credentials
Employees can change the email address they use to sign in and/or their password. The password section would only appear on programs that have usernames/password logins enabled so, for example, it would not appear with Single Sign-On setup.
Manage devices
Employees can see a list of all the devices where they're currently logged in and be able to log out a specific device or notify of an intrusion.
Recent Activity
Employees can see a list of the recent activity on the site that's related to security. They can see every time they log in, change their email address or password etc. If they find something unusual, they can use the same features as in the devices section to notify the intrusion.
Download Your Data
Employees can request a download of all the personal data we have, exercising their right to access under the GDPR (known as subject access).
The request is sent to a local data protection correspondent to verify the request is genuine, and then they will approve or deny it.
Employees will receive an initial email confirming their request has been acknowledged, and another email once the data is available to download.
.png)
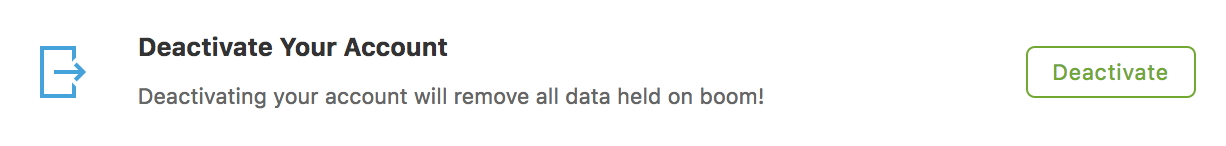
Deactivate Your Account
Employees can deactivate their account which permanently deletes all data related to the employee from our systems. This is a simple way for employees to exercise their right to erasure (sometimes referred to as ‘right to be forgotten’). A request is sent to our local data protection correspondent to verify the request is genuine and then approve or deny it. Once approved, all data is removed including any available cashback funds on account. You can read more detail about this process at the guide to Right to Erasure (Right to Erasure & Right to Access).
Where can employees find the Security Center?
In each employee’s 'My Account' section, there is a link to access the Security Settings. This would be under the normal General Settings link.
What can an employee do if they spot a device not recognized?
If a device is seen that looks suspicious, an employee can easily action this by clicking on the 'Not you?' link to start the process of securing their account. They will be taken to a page where more details of their device are shown and to confirm if they would like to 'Secure Account' as shown below:
If the 'Secure Account' button is clicked they'll automatically be logged out from this and all other devices, the suspicious activity will be blocked, preventing further access.
At this stage, to further enhance the security the employee has the option to 'Change Password'. They'll first be asked to verify their account and proceed to change their password.
Please note, this option is only available if the client has usernames and passwords on their program. If not, the account will be locked to prevent further unauthorized access.
What can someone do if they accidentally blocked their device?
If a device is blocked accidentally, all that needs doing is to unblock it by logging in to that device using the correct credentials.
When this is done, we will send an email containing a link to unblock the device. Once clicked, it counts as verification that the individual is the true owner of the device and it is re-activated.
How do we know what devices are being used?
We do this by adding a small cookie on the user's browser every time they log in. We use modern browser fingerprinting technologies to do this.

Comments
0 comments
Please sign in to leave a comment.